JWT Refresh Tokens: Rotation and Revocation
Managing JWT refresh tokens is all about balancing security with user convenience. Here's the deal:
- Access tokens provide short-term access (15–60 minutes) to resources.
- Refresh tokens allow users to get new access tokens without re-logging in and last 7–90 days.
- If refresh tokens are stolen, they pose serious risks. Two key strategies help mitigate this:
- Rotation: A new refresh token is issued every time you use the old one. This limits how long a stolen token can be used.
- Revocation: Tokens are invalidated immediately during events like logout or security breaches.
Rotation helps detect token misuse by flagging reused tokens, but it can strain system performance due to frequent database writes. Revocation ensures instant invalidation but requires infrastructure like Redis to track invalid tokens. Many systems combine both approaches for better security and efficiency.
To implement these strategies:
- Use short-lived access tokens (5–15 minutes).
- Store refresh tokens securely (e.g., HTTP-only cookies).
- Leverage tools like Redis for tracking and synchronization.
The choice between rotation, revocation, or both depends on your app's security needs and performance goals.
Refresh Token Rotation and Reuse Detection in Node.js JWT Authentication
sbb-itb-903b5f2
1. Token Rotation
Token rotation works by issuing a new refresh token every time an access token is exchanged, while immediately invalidating the old refresh token. This creates a constantly shifting target, making it harder for attackers to exploit stolen tokens.
Security Characteristics
One of the standout benefits of token rotation is its ability to detect when a token is reused. If an invalidated refresh token is presented, the authorization server flags it as a potential security breach. In response, it invalidates the entire token family and requires the user to re-authenticate. Kevin Gao, Head of Developer Relations at Descope, explains:
"Refresh token rotation is a security mechanism designed to minimize the risks associated with token theft and unauthorized use."
This approach significantly limits the time an attacker has to exploit a stolen token. Security experts also recommend setting an absolute session limit, such as 30 days, to further mitigate risks.
While these benefits enhance security, they come with operational challenges, particularly concerning performance.
Performance Impact
Unlike stateless JWTs, token rotation introduces a stateful element because it requires a database or cache write operation every time a refresh token is exchanged. This can strain high-traffic systems and may lead to race conditions when multiple requests occur simultaneously. To address this, you can implement client-side queuing using interceptors like Axios, which help limit concurrent requests.
For maintaining consistency in distributed environments, use tools like Redis or similar distributed caches instead of in-memory solutions. These ensure data persists even during server restarts and maintain consistency across multiple server instances.
Implementation Requirements
Implementing token rotation effectively involves three critical components: single-use enforcement, server-side tracking, and token family management. To protect against potential leaks, store hashed token metadata (e.g., using SHA-256) in your database instead of raw tokens. For web applications, secure tokens in HTTP-only, Secure cookies with the SameSite=Strict flag to mitigate XSS and CSRF attacks.
In systems with multiple microservices, opt for asymmetric signing algorithms like RS256 instead of HS256. This allows each service to verify tokens using a public key while keeping the private signing key secure. Modern frameworks, such as NextAuth and Passport.js, are increasingly adopting JWT rotation as a default behavior, aligning with OAuth 2.1 standards.
2. Token Revocation
Token revocation immediately disables tokens before their scheduled expiration. This is particularly useful for scenarios like user logout, password changes, or suspected security threats. Unlike token rotation, which replaces tokens regularly, revocation specifically halts the token's functionality.
Security Characteristics
A key challenge with JWTs is their self-contained design - once issued, they stay valid until they expire, without needing server validation. To counter this, revocation systems introduce server-side checks to determine if a token has been explicitly invalidated. One common method is token blacklisting, which saves the token's unique identifier (jti) in a high-speed cache like Redis. The blacklist entry remains until the token's natural expiration time.
For broader security needs, token versioning offers another approach. This method involves incrementing a stored user version during security events, or using a valid_since claim for timestamp-based revocation. Both effectively invalidate previously issued tokens. Software Engineer Ifeora Okechukwu Patrick explains the difference:
"Individual token revocation is strictly for refresh tokens, access tokens on the other hand should be invalidated in groups and never individually."
Performance Impact
Revocation introduces state into otherwise stateless JWT systems, which can create performance challenges. For instance, blacklisting requires a server-side check on every request, potentially adding latency. Using Redis can alleviate this, as it supports sub-millisecond lookups and automatic expiration (TTL), preventing the blacklist from becoming unmanageably large.
For even faster performance, probabilistic data structures like XOR filters or Bloom filters can provide quick revocation checks while using minimal memory. Among these methods, token versioning is the most efficient because it tracks one record per user rather than one per revoked token.
Implementation Requirements
To enable precise revocation tracking, every JWT should include a jti claim (a unique identifier). When blacklisting tokens in Redis, set the TTL to match the token's remaining lifetime for automatic cleanup. Use a Pub/Sub mechanism to propagate revocation events across all service instances, allowing them to update their local caches in real time without frequent network calls.
Best practices recommend access token lifetimes of 5–15 minutes for external APIs and up to 60 minutes for lower-risk internal services. Refresh tokens, on the other hand, typically last 7–14 days. This setup reduces the need for frequent database checks by focusing revocation efforts on long-lived refresh tokens while letting short-lived access tokens expire naturally.
Scalability Considerations
Different revocation strategies vary in speed, scalability, and complexity. The table below compares their performance:
| Strategy | Revocation Speed | Scalability | Complexity | Storage Cost |
|---|---|---|---|---|
| Token Blacklisting | Immediate | Good (with Redis) | Low | Medium |
| Short-Lived + Refresh | 5–15 minutes | Excellent | Medium | Low |
| Token Versioning | Immediate | Excellent | Low | Very Low |
| Introspection | Immediate | Poor | High | Low |
In distributed systems, revocation often depends on "eventual consistency." Regional blocklists or event-driven notifications help ensure all service instances receive revocation updates, though slight delays may occur. For timestamp-based revocation, include a small grace period (about 2 seconds) to account for clock drift across servers. For auditing purposes, mark tokens as "revoked" rather than deleting them outright, preserving a record for forensic analysis.
Advantages and Disadvantages
JWT Token Rotation vs Revocation: Security Strategies Compared
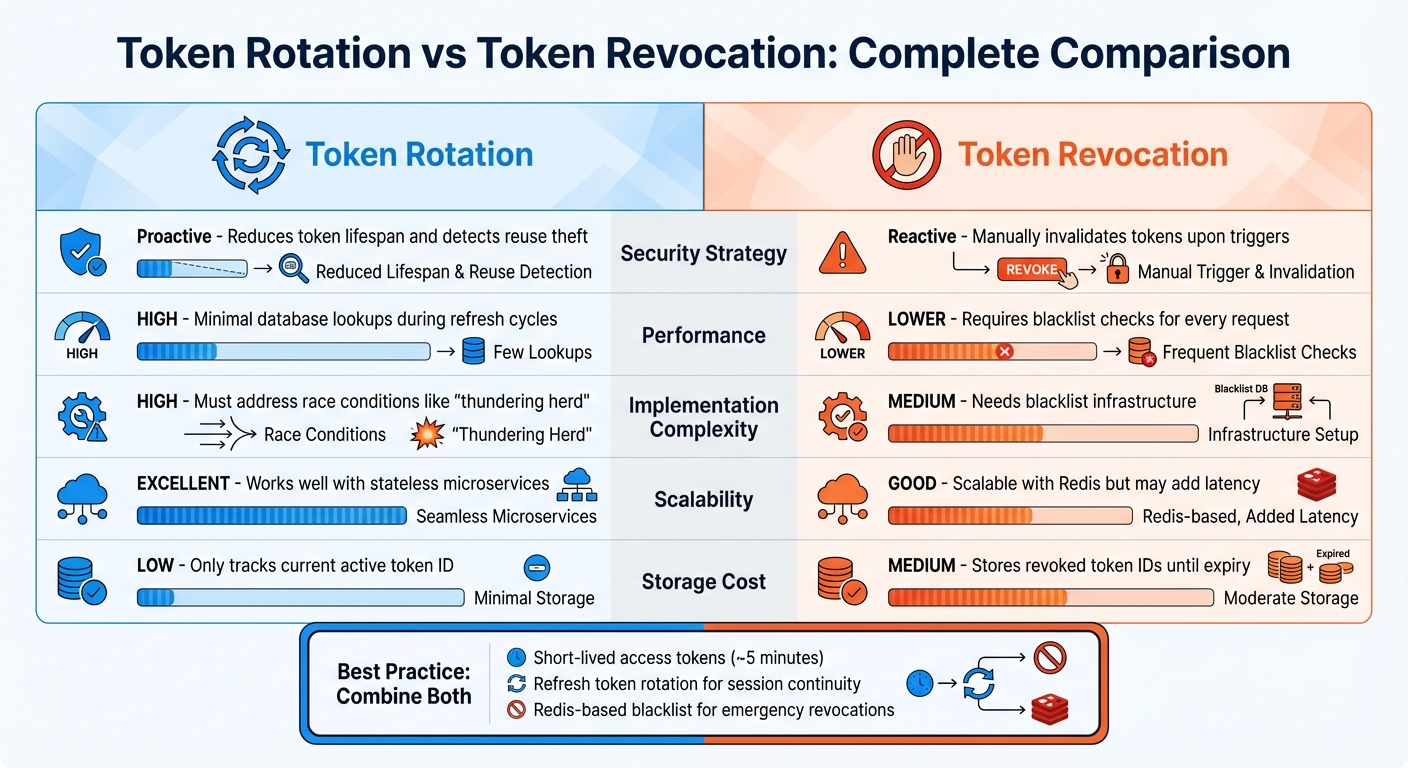
Building on the security mechanisms discussed earlier, this section dives into the practical trade-offs between token rotation and revocation.
Each method offers distinct benefits, but they come with different operational costs. Token rotation transforms static tokens into ones that are frequently updated, which reduces the time an attacker has to exploit a stolen token. On the other hand, token revocation provides immediate, manual control to invalidate tokens during specific events, such as user logouts or potential security breaches. As Devraj Patel, Founder & Identity Architect at SSOJet, points out:
"Reuse detection is the only way to stop an attacker who has successfully exfiltrated a long-lived token from a browser's local storage."
The differences between these approaches are not just about security - they also impact implementation and performance. Token rotation introduces challenges like managing race conditions, particularly the "thundering herd" problem, where simultaneous requests can cause multiple refresh attempts at once. Token revocation is easier to implement but requires infrastructure to manage blacklists or broadcast revocation events across distributed systems. These factors often shape the choice of method in system design.
Performance is another key consideration. Token rotation is largely stateless, requiring database interaction only during refresh cycles, which usually occur every 5–15 minutes. In contrast, blacklisting can slow down performance because it involves a lookup for every request. To strike a balance, many enterprises now adopt a hybrid approach. This typically involves using short-lived access tokens (lasting around 5 minutes) for better performance, refresh token rotation for session continuity, and a Redis-based blacklist for emergency revocations.
| Feature | Token Rotation | Token Revocation |
|---|---|---|
| Security Strategy | Proactive: Reduces token lifespan and detects reuse theft | Reactive: Manually invalidates tokens upon triggers |
| Performance | High: Minimal database lookups during refresh cycles | Lower: Requires blacklist checks for every request |
| Implementation Complexity | High: Must address race conditions like the "thundering herd" | Medium: Needs blacklist infrastructure |
| Scalability | Excellent: Works well with stateless microservices | Good: Scalable with Redis but may add latency |
| Storage Cost | Low: Only tracks the current active token ID | Medium: Stores revoked token IDs until expiry |
This comparison highlights that neither approach is universally better - it all depends on the specific needs and constraints of the system in question.
Conclusion
Token rotation and token revocation each play a critical role in securing sessions, with distinct strengths tailored to different scenarios. Token rotation works proactively, reducing the risk of stolen credentials by limiting their usability and identifying theft through reuse patterns. On the other hand, token revocation provides a reactive approach, allowing for immediate session termination in cases like password resets or suspected breaches.
Choosing the right approach depends on your application's needs. For example, if you're developing a single-page application that must handle sessions across browser privacy restrictions, token rotation is likely the better option. But if your focus is on instant "logout everywhere" functionality, token revocation with versioning offers an efficient solution. Many production systems blend these approaches, using short-lived access tokens (about 5 minutes), refresh token rotation for seamless session management, and a Redis-based blacklist for emergencies. This hybrid approach balances the performance benefits of stateless tokens with strong security measures.
Each method comes with its own challenges. Token rotation involves managing race conditions and tracking active tokens within token families. Token revocation, meanwhile, requires storage infrastructure to maintain a list of invalidated tokens until they naturally expire. Your system's specific requirements - like storage capacity, implementation complexity, and security priorities - will guide your decision.
Whichever strategy you choose, it's essential to monitor for token reuse and automate the cleanup of expired tokens. These practices are fundamental to maintaining a secure and efficient session management system, whether you rely on rotation, revocation, or a combination of both.
FAQs
When should I use rotation vs revocation?
To improve security, implement rotation by issuing a new refresh token every time the current one is used. This approach minimizes the chances of stolen tokens being reused. On the other hand, revocation is useful for instantly invalidating tokens, such as in cases of suspected compromise or when a user logs out. This can be achieved using methods like a denylist or a versioning system. Rotation strengthens long-term security, while revocation handles immediate threats effectively.
How do I handle refresh-token race conditions?
To handle refresh-token race conditions effectively, implement refresh token rotation. This approach ensures that each refresh token is replaced with a new one after use, making it harder for attackers to exploit replay attacks. Server-side checks should also invalidate any old tokens once a new one is issued.
Another useful method is maintaining a token revocation list on the server. This list tracks and blocks tokens that have been reused or marked invalid. To strengthen security further, follow these best practices: keep access token lifespans short, use single-use refresh tokens, and verify tokens server-side with every request.
What’s the safest way to store refresh tokens in browsers?
The best way to keep refresh tokens secure in browsers is by using HttpOnly, Secure, and SameSite cookies. These settings block JavaScript from accessing the tokens, significantly lowering the risk of XSS attacks. On top of that, using refresh token rotation strengthens security further by regularly updating tokens, making them much harder to misuse if they ever get compromised.